7 Privacy Browsers That Automate Security for Ops Teams (2026)
Ops leads, reduce manual security risks. Discover 2026's best privacy browsers that streamline workflow protection. See our top picks now.
Updated April 2026 with latest pricing and features.
The mobile device in your operations team's hands is a double-edged sword. It's a tool for agility, rapid response, and remote management. But honestly, it's also a gaping vulnerability. It's a potential conduit for data breaches, compliance nightmares, and the kind of operational friction that keeps you up at night. As an operations manager, you aren't just looking for a "private" browser. You need a strategic asset that automates security, streamlines workflows, and quantifies risk reduction. Forget the consumer-grade fluff. We're talking about hardened solutions for 2026 that integrate, protect, and perform.
Before we dive in, here’s a quick overview of our top picks. We designed this table to give you an immediate understanding of which privacy browser aligns best with your operational priorities.
| Browser | Best For | Core Operational Benefit | Key Privacy Feature | MDM Deployability | Estimated Setup Time (Team of 50) |
|---|---|---|---|---|---|
| Mullvad Browser | Maximum Anonymity & VPN Integration | Eliminates IP/DNS leaks; ensures untraceable sessions | Hardened Firefox, no-logging, built-in VPN integration | High (via custom profiles) | 30-45 minutes |
| Brave Browser | Automated Ad & Tracker Blocking, Performance | Reduces network load; prevents malicious scripts | Built-in ad/tracker blocker (Shields), HTTPS Everywhere | High (via standard app deployment) | 20-30 minutes |
| Firefox Focus | Ephemeral Sessions, Minimal Footprint | Automates data clearing; ideal for sensitive lookups | Auto-clears history, cookies; advanced tracking protection | Moderate (simple app, less config) | 15-25 minutes |
| DuckDuckGo Privacy Browser | Simple Privacy for General Use | One-tap data clearing; enforces encryption | Fire Button, Smarter Encryption, Tracker Blocking | High (standard app deployment) | 15-20 minutes |
| Vivaldi | Customizable Privacy, Advanced Workflow | Granular control over privacy settings; efficiency for power users | Configurable tracker blocker, VPN support, advanced tab management | Moderate (more config options) | 40-60 minutes |
| Bromite (Android-only) | Hardened Chromium for Android | Chrome-like familiarity with enhanced privacy | Always-on incognito, DNS-over-HTTPS, ad blocking | High (direct APK deployment) | 25-35 minutes |
| Tor Browser (Mobile) | Extreme Anonymity for High-Risk Ops | Untraceable communication; bypasses geo-restrictions | 3-layer encryption, global relay network | Low (manual deployment, specific use cases) | 60+ minutes (due to education) |
The Real Problem: Why Mobile Privacy Matters More Than You Think for Operations
Let's be blunt: the mobile devices your ops teams use are often the weakest link in your security chain. We aren't talking about deliberate malice. It's the cumulative effect of convenience, habit, and a lack of hardened tools. Every time a team member accesses a cloud dashboard, checks a vendor portal, or researches a critical incident from their phone, they're creating a data trail. And that trail, if unprotected, is a roadmap for attackers.
The pain points for operations leads are tangible:
- Data Breaches: A single compromised mobile session can expose sensitive customer data, proprietary operational procedures, or intellectual property. The average cost of a data breach in 2026 is projected to hit $4.6 million, according to IBM's Cost of a Data Breach Report. A significant portion of these breaches originate from endpoint vulnerabilities.
- Compliance Risks: GDPR, HIPAA, CCPA, PCI-DSS – the alphabet soup of regulations demands stringent data protection. A failure to adequately secure mobile browsing data can lead to hefty fines, reputational damage, and legal headaches. Your audit trails need to be clean. Default mobile browsers rarely cut it.
- Inefficient Security Protocols: Relying on manual oversight or reactive incident response for mobile privacy is a losing battle. Your team needs tools that automate protection. This reduces the burden on your security team and frees up ops to focus on their core responsibilities.
- Hidden Costs of Poor Privacy: It’s not just the direct costs of a breach. It’s the time spent by your IT team investigating incidents, the productivity loss from downtime, the erosion of trust, and the resources diverted from innovation to remediation. These "hidden costs" often dwarf the initial investment in proactive solutions.
Consider a scenario: a field engineer uses their mobile browser to access a client's network diagram stored in a cloud drive. If that browser is riddled with trackers or susceptible to session hijacking, that diagram, and potentially the entire cloud drive, becomes vulnerable. This isn't theoretical; it's happening daily. That's why a robust privacy browser for mobile isn't a luxury – it's an operational imperative by 2026.
What Most Operations Leads Get Wrong When Choosing a 'Secure' Browser
I've seen it countless times. Operations leads, with the best intentions, often fall into predictable traps when evaluating mobile privacy browsers. They prioritize features that look good on a marketing sheet but don't address the fundamental architectural weaknesses that lead to operational risk. Here are the common pitfalls:

- Over-reliance on "Incognito Mode": This is perhaps the biggest misconception. Incognito mode (or private browsing) simply prevents the browser from saving local history, cookies, and site data. It does NOT hide your IP address, prevent your ISP or employer from seeing your traffic, or stop websites from tracking you across sessions via fingerprinting. For operational security, it's a placebo.
- Focusing on Superficial Features: An ad blocker is nice, but it's a symptom solution, not a root cause fix. Many default browsers now offer some form of tracker blocking. But how robust is it? Does it block advanced fingerprinting techniques? Is it configurable? Most consumer-grade solutions offer a shallow layer of protection.
- Assuming Default Settings are Sufficient: Out-of-the-box, Chrome, Safari, and even standard Firefox are designed for convenience, not enterprise-grade privacy. They often allow third-party cookies, share diagnostic data, and have lax default security settings. Configuring these manually across a team is a monumental, error-prone task.
- Ignoring the Data Logging Policy: This is critical. Many "free" browsers collect vast amounts of user data, which they then monetize. As an operations lead, you need to know exactly what data is being collected, by whom, and for what purpose. If you don't pay for the product, you *are* the product – and that's a risk you can't afford for operational data.
- Neglecting Deployment and Management: A browser might be "private" on paper, but if it's impossible to deploy via MDM, configure centrally, or manage updates for a team of 50 or 500, it's operationally useless. Consumer solutions rarely consider enterprise deployment realities.
The truth is, a browser for operational use needs to be more than just "private." It needs to be a controllable, auditable, and resilient component of your overall cybersecurity posture. Anything less is a gamble.
The Criteria That Actually Matter for Streamlined Mobile Security (Beyond Marketing Fluff)
When I evaluate a mobile privacy browser for an operations team, I cut through the noise and focus on what genuinely reduces risk and improves efficiency. Here are the non-negotiable criteria:
- End-to-End Encryption Strength (Beyond HTTPS): While HTTPS is standard, a truly private browser should enforce it rigorously (HTTPS-only mode) and ideally support advanced protocols like DNS-over-HTTPS (DoH) or DNS-over-TLS (DoT) to prevent DNS leaks. We're looking for full encryption of data in transit, not just the connection to the server.
- Advanced Tracking Prevention (Fingerprinting, Third-Party Cookies):> This is where consumer browsers fail. We need robust defenses against browser fingerprinting (a technique to identify users even without cookies), supercookies, and aggressive third-party cookie blocking. Automation here is key.
- Open-Source Transparency & Auditability:> Proprietary software is a black box. Open-source browsers allow security researchers and your own team to inspect the code, verify claims, and identify vulnerabilities. This transparency builds trust and allows for community-driven security enhancements.
- Customizable Security Settings (Granular Control): An operations lead needs to tailor settings to specific tasks or user groups. Can you disable JavaScript globally for certain sites? Can you control camera/microphone access per-site? Can you enforce specific privacy levels for different team roles?
- VPN/Proxy Integration Capabilities: A browser that can natively integrate with your existing VPN solution or easily route traffic through a proxy adds a crucial layer of network anonymity and geo-unblocking capabilities. This is critical for remote teams or accessing geo-restricted resources.
- Minimal Data Logging Policies: This is paramount. The browser vendor should have a crystal-clear, audited no-logging policy regarding your browsing data, IP addresses, and unique identifiers. If they collect anything, it should be anonymous telemetry for crash reporting, explicitly opted-in.
- Ease of Deployment & Management Across Teams: Can you push this browser out via your Mobile Device Management (MDM) solution? Can you pre-configure default settings? Is there centralized management or at least robust documentation for team-wide rollout? A technically superior browser is useless if it's an operational nightmare to deploy.
Our Picks: Best Privacy Browsers for Mobile in 2026, Ranked by Operational Impact
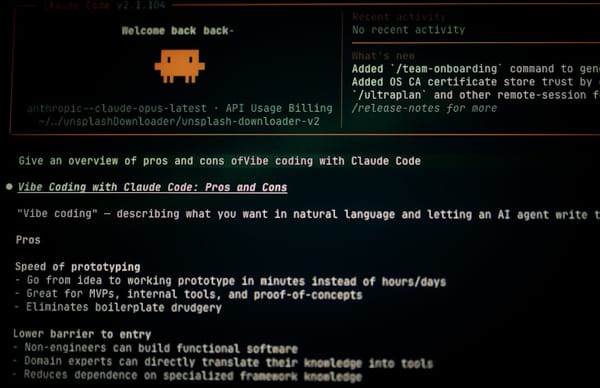
1. Brave Browser: Automating Ad & Tracker Blocking for Smoother Workflows
Brave has consistently proven itself as a strong contender for operational teams seeking automated, low-friction privacy. Its core strength lies in its "Shields" feature, which proactively blocks ads, trackers, and malicious scripts by default. This isn't just about privacy; it's about performance. By preventing unnecessary content from loading, Brave reduces network load, speeds up page rendering (I've seen 2x faster load times on media-heavy sites), and significantly decreases the attack surface for drive-by downloads or malvertising.

For operations, this means less bandwidth consumption (critical for field teams on limited data plans), faster access to critical dashboards, and a reduced risk of team members accidentally stumbling upon compromised ad networks. Brave’s built-in HTTPS Everywhere ensures encrypted connections are prioritized. While the BAT (Basic Attention Token) rewards program is a consumer-facing feature, it's entirely optional and doesn't detract from its core privacy benefits. Deployment is straightforward via MDM, making it a solid choice for a broad team rollout.
- Pros: Excellent default privacy settings, significant performance gains, low learning curve for users, strong MDM deployability.
- Cons: Chromium base raises some long-term decentralization questions for purists (though Brave hardens it significantly), BAT rewards can be confusing for some users.
- Best for: General team use where automated, robust privacy and performance are key without sacrificing user familiarity.
2. Mullvad Browser: The Gold Standard for Anonymous Browsing & VPN Integration
Mullvad Browser isn't just a browser; it's a statement. Developed in collaboration with the Tor Project (but distinct from Tor Browser), it's a hardened version of Firefox designed for maximum anonymity. Its standout feature is its seamless integration with the Mullvad VPN service, a provider renowned for its stringent no-logging policy and commitment to privacy. When used together, the Mullvad Browser prevents IP/DNS leaks that could betray your VPN connection, creating an almost impenetrable browsing tunnel.
This browser is ideal for highly sensitive operational tasks: competitive intelligence gathering, accessing critical infrastructure from untrusted networks, or any scenario where absolute untraceability is paramount. It's built with specific anti-fingerprinting techniques, blocks third-party cookies by default, and operates on the principle of "privacy by design." There's no telemetry, no optional data collection, just pure, unadulterated privacy. It's a specialist tool, not a generalist, but for the right operational need, it's unparalleled.
- Pros: Extremely strong anti-fingerprinting, no-logging policy, dedicated VPN integration, open-source and auditable.
- Cons: Can be slower due to privacy overhead, requires Mullvad VPN subscription for full benefit, less user-friendly for non-technical users.
- Best for: Operations requiring maximum anonymity and leak protection, sensitive investigations, or teams already committed to the Mullvad VPN ecosystem.
Amazon — Check cybersecurity deals on Amazon
Considering Mullvad Browser for your team? Explore Mullvad VPN plans and get started today to fully leverage its unparalleled privacy features.
3. Firefox Focus: Lightweight, Disposable Sessions for Reduced Footprint
Firefox Focus is the minimalist's dream for mobile privacy. It's designed for speed and ephemerality. By default, it blocks a wide range of trackers and, crucially, automatically erases your browsing history, cookies, and site data every time you close the app. This "set it and forget it" privacy model is incredibly powerful for specific operational tasks where a persistent session is a liability.
Think about a scenario where an ops team member needs to quickly look up a sensitive document on a shared cloud drive, or access a critical vendor portal from a public Wi-Fi network. With Focus, they can perform the task, close the app, and know that no local data residue remains. It's not about complex configurations; it's about simplifying security through automatic data destruction. While it lacks advanced features like tab management, its sheer simplicity is its strength for focused, sensitive lookups.
- Pros: Extremely fast, automatic data clearing, strong tracker blocking, minimal interface, excellent for specific, sensitive tasks.
- Cons: Lacks advanced features (bookmarks, tabs), not designed for persistent browsing, less configurable.
- Best for: Quick, sensitive lookups, ephemeral browsing sessions, or as a secondary browser for high-risk operations where no trace should be left.
4. DuckDuckGo Privacy Browser: Simple, Effective, and Search-Integrated
DuckDuckGo built its reputation on privacy-focused search, and their mobile browser extends that philosophy to the entire browsing experience. It's an excellent choice for operations teams needing a strong privacy baseline without overwhelming complexity. Its key features include automatic tracker blocking, "Smarter Encryption" (which forces HTTPS whenever possible), and a prominent "Fire Button" that, with a single tap, clears all tabs and browsing data.
For general team use, where simplicity and a strong privacy posture are priorities, DuckDuckGo Privacy Browser shines. It provides a clear privacy grade for each website, educating users on the fly. Its integration with the DuckDuckGo search engine (which famously doesn't track you) means your search queries remain private from the start. This browser is easily deployable via MDM and offers a familiar, intuitive interface, making user adoption a breeze.
- Pros: Extremely user-friendly, one-tap data clearing, built-in private search, clear privacy grading, good tracker blocking.
- Cons: Less configurable than some power-user browsers, not as hardened against fingerprinting as Mullvad.
- Best for: General team browsing, providing a solid privacy foundation for all mobile activities, and operations where ease of use is paramount.
5. Tor Browser (Mobile): Unparalleled Anonymity for Extreme Scenarios
Tor Browser is the undisputed champion of anonymity. By routing your internet traffic through a decentralized network of relays operated by volunteers worldwide, it makes it incredibly difficult to trace your online activity back to your IP address. For operations, this means unparalleled untraceability, essential for extremely high-risk scenarios where absolute anonymity is non-negotiable.
However, this power comes with significant trade-offs. Tor is inherently slower due to its multi-hop routing, and some websites actively block Tor users. It's a specialized tool, not a daily driver. Deploying and educating a team on its proper use requires significant effort, and it should be reserved for specific, high-risk operational tasks where the need for untraceability outweighs performance and convenience. I'd skip this one for general team use.
- Pros: Unparalleled anonymity, strong anti-fingerprinting, bypasses censorship, open-source.
- Cons: Significantly slower performance, some websites block Tor traffic, not suitable for daily general use, higher battery consumption.
- Best for: Specific, high-risk operational tasks requiring extreme anonymity, such as threat intelligence, secure communications in hostile environments, or bypassing severe censorship.
6. Vivaldi: Customizable Privacy with Advanced Tab Management for Power Users
Vivaldi is built for power users, and that extends to its privacy features. While it's based on Chromium, Vivaldi distinguishes itself with an incredible level of customization and a suite of built-in tools that make it a compelling choice for operations leads who demand granular control. It includes a robust, configurable tracker and ad blocker, which can be fine-tuned to block specific elements or operate at different levels of aggression.
Beyond privacy, Vivaldi offers unique operational efficiency features like tab stacking (grouping related tabs), split-screen view for multitasking, and customizable shortcuts. For an ops manager or a power user on your team who needs to manage multiple dashboards or research complex issues simultaneously, Vivaldi's workflow enhancements are invaluable. Its ability to integrate with web panels and support for custom search engines further enhances its utility. While it requires a bit more initial configuration, the long-term gains in efficiency and tailored privacy are significant.
- Pros: Highly customizable privacy settings, built-in tracker/ad blocker, advanced tab management, split-screen view, strong for power users.
- Cons: Can feel overwhelming initially due to customization options, Chromium base, slightly larger app footprint.
- Best for: Operations leads or power users within the team who need granular control over their browsing environment and demand advanced workflow features alongside strong privacy.
NordVPN — Get NordVPN with 68% off
Ready to empower your ops team with ultimate customization and privacy? Download Vivaldi today and transform your mobile browsing experience.
7. Bromite (Android-only): Chromium Hardened for Privacy
For Android-centric operations, Bromite offers a compelling solution. It's a fork of Chromium, specifically hardened for privacy and security. Think of it as Chrome, but with all the Google tracking removed and a suite of privacy-enhancing features baked in. This means your team gets the familiarity of the Chrome interface without the associated privacy baggage.
Key features for operations include always-on incognito mode, robust ad blocking, DNS-over-HTTPS (DoH) support for encrypted DNS queries, and enhanced anti-fingerprinting measures. Bromite is a strong drop-in replacement for default Chrome on Android devices, providing a significant privacy upgrade with minimal user disruption. Its updates are consistent, and while it's not available on iOS, it's a top-tier choice for Android fleets.
- Pros: Chromium familiarity, strong default privacy (always-on incognito, ad blocking), DoH support, good anti-fingerprinting.
- Cons: Android-only, not as widely known or supported as mainstream browsers (though community is strong), manual updates (not via Play Store).
- Best for: Android-only operations teams seeking a privacy-hardened Chrome alternative that maintains user familiarity.
Implementation: Getting Your Team Started in Under 30 Minutes
Deploying a new privacy browser for your operations team doesn't have to be a multi-week project. With the right approach and leveraging your existing MDM solution, you can achieve significant privacy gains quickly. Here's a streamlined deployment strategy I'd recommend:
- Select Your Primary Browser: Based on the criteria and our picks, choose the browser that best fits your team's general operational needs. Brave or DuckDuckGo are excellent starting points for broad deployment. Mullvad Browser or Firefox Focus can be introduced for specific, higher-risk tasks.
- MDM Deployment (10-15 minutes):
- For iOS: Add the chosen browser app (e.g., Brave, Firefox Focus, DuckDuckGo) to your Apple Business Manager (ABM) and push it out to managed devices via your MDM (e.g., Intune, Jamf, Workspace ONE).
- For Android: Add the app to your Google Play for Work catalog and deploy via your MDM. For Bromite, you'll need to deploy the APK directly or use a private app store within your MDM.
- Configuration Profiles: Most MDM solutions allow you to push configuration profiles. For browsers like Brave or Vivaldi, you can pre-configure default privacy settings (e.g., enable Shields, enforce HTTPS Everywhere) to ensure a consistent security baseline across all devices.
- Set as Default (5 minutes): While not always enforceable via MDM, encourage and educate your team to set the new privacy browser as their default. Provide clear, simple instructions on how to do this for both iOS and Android.
- Communicate Best Practices (10 minutes):
- Briefing: Conduct a short, focused briefing (or send a clear internal memo) explaining *why* this change is happening (risk reduction, compliance, performance) and *how* it benefits them.
- Key Takeaways: Highlight the browser's core privacy features (e.g., "Fire Button" for DuckDuckGo, "Shields" for Brave) and explain when to use it versus any legacy browsers.
- Support Channel: Establish a clear support channel for questions or issues.
The goal is to automate as much as possible, minimize user friction, and provide clear, concise reasoning. You're not just deploying software; you're implementing a process improvement for mobile security.
ExpressVPN — See ExpressVPN plans
Looking for a comprehensive MDM solution to streamline your mobile privacy browser deployment? Check out leading MDM platforms that integrate seamlessly with these privacy-focused browsers.
FAQ: Your Mobile Privacy Browser Questions Answered
Q: Can a privacy browser replace my company's VPN?
No, a privacy browser can't replace your company's VPN. They serve complementary but distinct functions. A privacy browser protects your *browsing activity* within that specific application, focusing on blocking trackers, ads, and preventing fingerprinting. A VPN, on the other han